Client-Initiated Backchannel Authentication (CIBA) does not rely on a client application redirecting the user via the browser to perform the login/authentication process. Instead, the client application directly calls the Provider via a backchannel request to initiate the authentication flow. The following sequence diagram illustrates an implementation of the CIBA Flow:Documentation Index
Fetch the complete documentation index at: https://auth0-cq3uo.mintlify.app/llms.txt
Use this file to discover all available pages before exploring further.
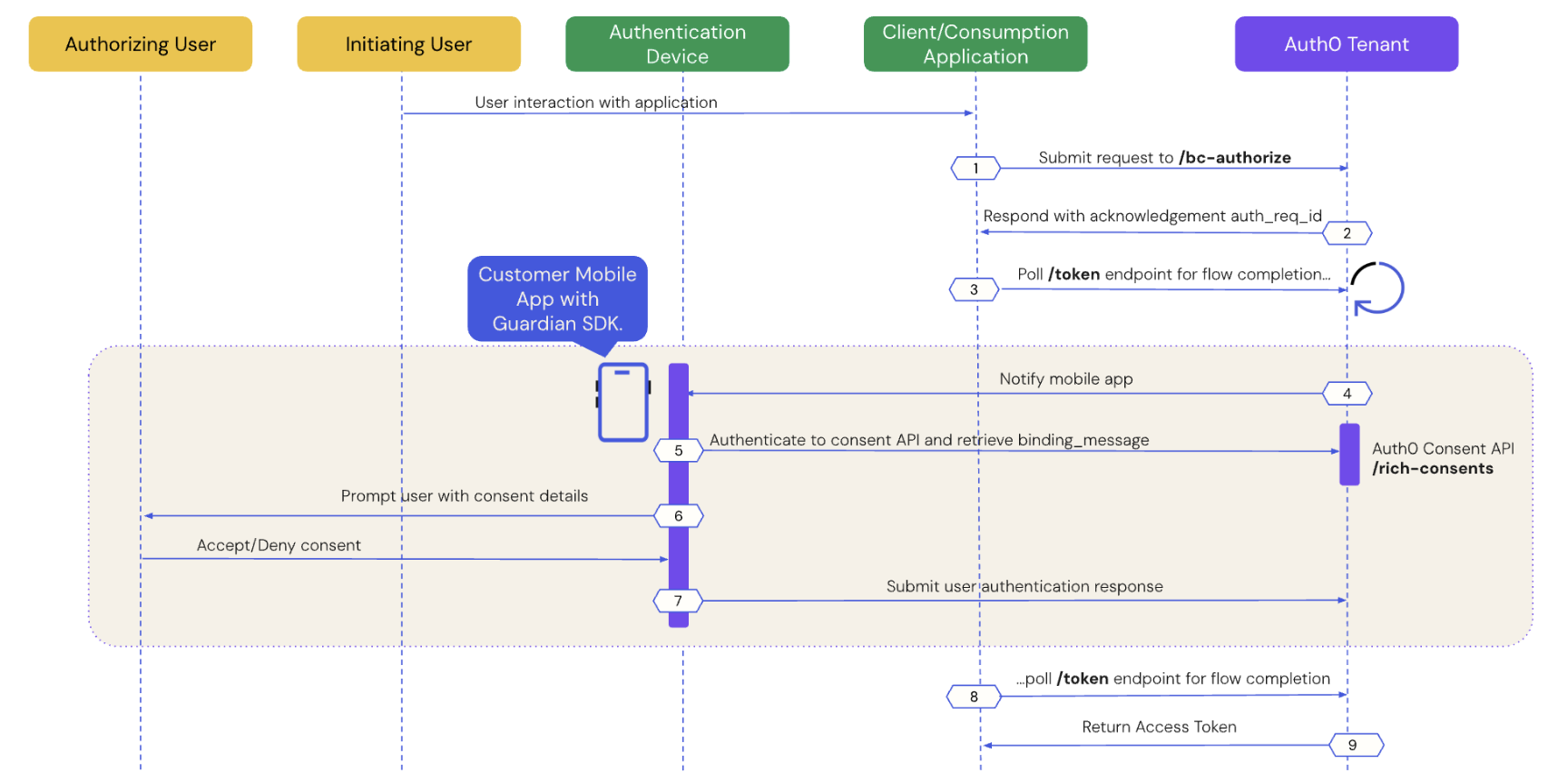
- Prerequisites
- Step 1: Client application initiates a CIBA request
- Step 2: Auth0 tenant acknowledges the CIBA request
- Step 3: Client application polls for a response
- Step 4: Mobile application receives the push notification
- Step 5: Mobile application retrieves the consent details
- Step 6: Mobile application presents the consent details to the user
- Step 7: Mobile application sends the user response back to Auth0
- Step 8: Auth0 receives user response after the flow completes
- Step 9: Auth0 returns access token to client application
Prerequisites
To initiate a CIBA push request using Auth0, you must complete the following prerequisites:- Integrate your custom mobile application with the Guardian SDK. To learn more, read Configure Client-Initiated Backchannel Authentication.
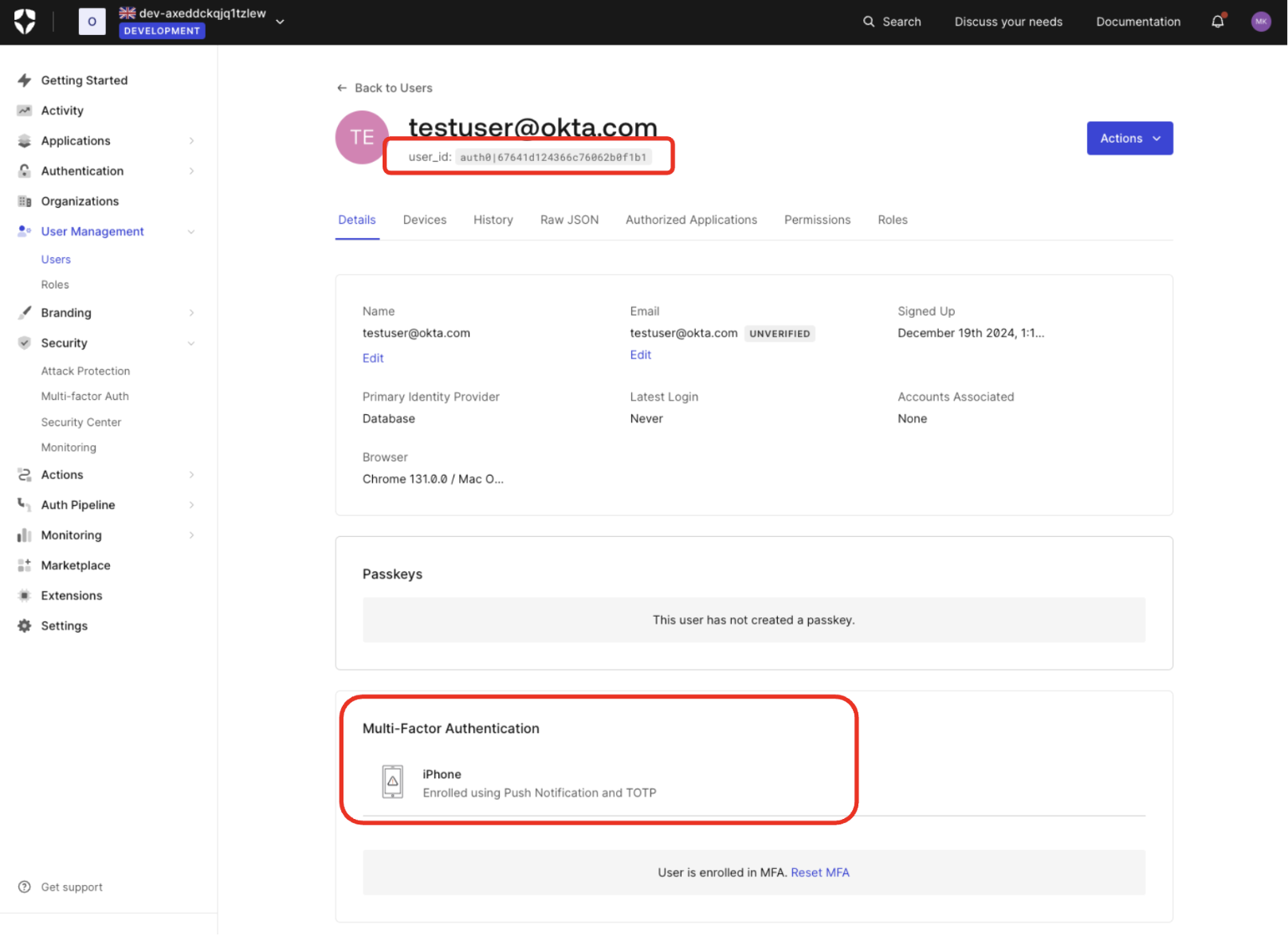
- Enroll the authorizing user in MFA using push notifications via the Guardian SDK. To verify in the , navigate to User Management > Users and click on the user:
- Configure Client-Initiated Backchannel Authentication for your tenant and application.
Step 1: Client application initiates a CIBA request
Use the User Search APIs to find the authorizing user for whom you’d like to initiate a CIBA request and obtain their user ID. Once you have a user ID for the authorizing user, use the Authentication API or our SDKs to send a CIBA request to the/bc-authorize endpoint:
- cURL
- C#
- Go
- Java
| Parameters | Description |
|---|---|
tenant | Tenant name. It can also be a custom domain. |
client_id | Client application identifier. |
client_secret | Client authentication method used for user authentication with CIBA, such as Client Secret, Private Key JWT, or mTLS Authentication. If you’re using Private Key JWT or mTLS, you don’t need to include the client secret. |
scope | Must include openid.The scope can optionally include offline_access to request a refresh token. However, for one-time authorization of a transaction with the CIBA Flow, a refresh token is not needed and does not have any meaning in this context. |
user_id | User ID for the authorizing user that is passed within the login_hint structure. If iss_sub format is used, then the user ID is passed within the sub claim.The user ID for a federated connection may have a different format. |
request_expiry | The CIBA flow’s requested expiry is between 1 and 300 seconds, and it defaults to 300 seconds. Include the request_expiry parameter to set a custom expiry for the CIBA flow. |
binding_message | Human-readable message used to bind the CIBA flow across the authentication and consumption devices. The binding message is required and up to 64 characters. Use only alphanumeric and +-_.,:# characters. |
There is a user-specific rate limit where the authorizing user will not be sent more than 5 requests per minute.
Step 2: Auth0 tenant acknowledges the CIBA request
If the Auth0 tenant successfully receives thePOST request, you should receive a response containing an auth-req-id that references the request:
auth_req_id value is passed to the /token endpoint to poll for the completion of the CIBA flow.
Step 3: Client application polls for a response
Use the Authentication API or our SDKs to call the/token endpoint using the urn:openid:params:grant-type:ciba grant type and the auth_req_id you received from the /bc-authorize endpoint:
- cURL
- C#
- Go
- Java
/token endpoint.
Step 4: Mobile application receives the push notification
Auth0 sends a push notification to the user’s registered mobile app or device. The Guardian SDK provides methods to parse the data received from the push notification and return a ready-to-useNotification instance. The Notification instance includes a transaction linking ID, or txlinkid, that the mobile application uses to retrieve the consent details from Auth0.
The following code samples are example iOS and Android mobile push notification implementations using the Guardian SDK:
- iOS
- Android
Step 5: Mobile application retrieves the consent details
Call the Guardian SDK from your mobile application to retrieve the consent details i.e. the contents of thebinding_message from the Auth0 Consent API.
The following code samples are example iOS and Android implementations that retrieve data from the Auth0 Consent API:
- iOS
- Android
Step 6: Mobile application presents the consent details to the user
The Auth0 Consent API responds to the mobile application with the consent details, including thebinding_message, scope, and audience. The scopes returned to the mobile application are filtered according to your RBAC policy. To learn more, read Role-Based Access Control.
The mobile application presents the authentication request and/or the consent details to the user.
The following code sample is an example response from the Auth0 Consent API:
Step 7: Mobile application sends the user response back to Auth0
Depending on whether the user accepts or rejects the authentication request, the mobile application sends the user response back to Auth0. The following code samples are example iOS and Android implementations that handle the user response:User accepts the authentication request
- iOS
- Android
User rejects the authentication request
- iOS
- Android
Step 8: Auth0 receives user response after the flow completes
The client application completes the polling upon receiving a response from the/token endpoint. A CIBA flow always requires a response, either an approval or decline, from the authorizing user, and existing grants are not checked.
Step 9: Auth0 returns access token to client application
If the user rejects the push request, Auth0 returns an error response like the following to the client application:id_token will only be present if the openid scope was included in the initial /bc-authorize request.

